Ethical hacking reframes cybersecurity as proactive risk management. It relies on authorized, attacker-like testing to uncover real flaws before harm occurs. This practice operates within clear legal and ethical boundaries and emphasizes transparent disclosure and accountable remediation. By simulating threats, organizations gain practical fixes and stronger defenses. The approach is disciplined and evolving, balancing technical rigor with governance. It invites ongoing evaluation as threats shift and standards shift, leaving a practical question lingering for stakeholders.
What Ethical Hacking Really Is and Why It Matters
Ethical hacking refers to the practice of assessing the security of computer systems, networks, and applications with permission from the owners, using techniques that mirror those of malicious actors to identify and remediate vulnerabilities.
It clarifies boundaries between risk and trust, emphasizing accountability and continuous improvement.
The approach supports reputation management by demonstrating diligence, while responsible disclosure ensures timely, ethical remediation and information sharing.
How Ethical Hackers Think Like Attackers to Find Real Fixes
By examining systems through the lens of an attacker, ethical hackers translate potential exploits into concrete defenses, mapping how threats could unfold from initial access to impact. They cultivate a penetration mindset, rigorously testing controls and prioritizing real fixes over theory.
Through attacker simulation, the process reveals gaps, informs secure designs, and reinforces responsible, transparent defense strategies that empower freedom and trust.
From Laws to Ethics: Navigating the Rules of Safe, Legal Testing
Navigating the boundary between curiosity and responsibility, the discussion examines how laws and ethics shape safe, legal testing in cybersecurity. This section analyzes governance, compliance frameworks, and professional standards guiding researchers while preserving freedom to explore. It highlights privacy pitfalls and liability concerns, emphasizing transparent protocols, documented scope, and responsible disclosure as essential practices for trustworthy, lawful security testing.
Building a Practical Path: Skills, Roles, and Getting Started in the Field
What concrete steps, skills, and roles constitute a practical path into the field of ethical hacking, and how can newcomers translate curiosity into a structured career plan?
The path blends foundational security literacy, hands on labs, and progressive certification.
Roles include tester, analyst, and defender.
Career pathways emphasize ethical practice, continuous learning, and real-world simulations, with transparent milestones and disciplined, lawful advancement.
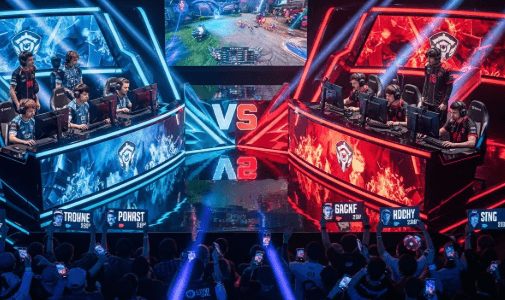
See also: The Rise of Esports Industry
Frequently Asked Questions
What Certifications Are Most Valued in Ethical Hacking Today?
The most valued ethical hacking certifications include CEH, OSCP, CISSP, and GPEN, recognized for demonstrating practical skills and risk awareness. They support career progression, signaling competence, integrity, and ongoing commitment to transparent, responsible cybersecurity practice in freedom-focused roles.
How Long Does It Take to Become a Proficient Ethical Hacker?
Proficiency in ethical hacking emerges over several years of dedicated study and hands-on practice, varying with prior IT experience. Career progression depends on consistent learning, certification milestones, and practical security project work, yielding gradual, transparent professional advancement.
What Are Common Career Paths After Certifications?
Career transitions after certifications include specialized roles in security operations, pentesting leadership, and threat intelligence, delivering ethical advantages through rigorous risk analysis. They pursue continuous learning, maintaining transparent responsibilities, while embodying freedom-minded professionals navigating regulated, methodical career paths.
How Do Bug Bounty Programs Differ From Internal Pen-Testing?
Bug bounty programs reward external researchers for disclosed flaws, while internal pen-testing relies on authorized employees to assess systems; bug bounty dynamics emphasize external disclosure, whereas internal testing contrasts with controlled environments, scope, and risk management.
What Are Typical Daily Tasks of a Security Tester?
Is daily practice repetitive or strategic for a tester? A security tester performs planning, asset inventory, vulnerability scanning, threat modeling, proof-of-concept testing, documentation, report generation, remediation validation, and ongoing cyber hygiene improvements, with transparent, methodical risk-focused communication.
Conclusion
Ethical hacking embodies disciplined curiosity: probing systems with consent to uncover weaknesses before adversaries do. The practice blends legality, ethics, and methodical testing to build robust defenses and trust. As one practitioner recalls, a single misconfigured port learned through controlled probing saved a major retailer from a costly breach, like a lighthouse revealing hidden shoals. Data shows organizations engaging in regular, authorized testing reduce incident costs and durations. In this evolving landscape, transparent, responsible testing remains essential to resilience.